With more and more of our daily lives moving online, staying safe when browsing is now more important than ever. Browser hijackers are an increasingly common threat, aiming to disrupt your browsing experience and compromise your privacy. This article will discuss exactly how browser hijackers work, the issues that they cause, how you can spot these and how you can remove them across various devices and browsers.
What is a browser hijacker?
A browser hijacker is a form of malicious software that has been designed to modify the internet browser settings of the infected device without the knowledge, or consent, of the user.
The most common changes are browser hijacker will make is the changing of your homepage, default search engine and new tab settings, often employed to redirect the user to unwanted websites. This allows the hacker to generate revenue through advertising and traffic redirection.
On some occasions, certain browser hijackers may also stealthily collate browsing data and sensitive personal information in the background that can later be used for malicious purposes such as demanding ransom payments to avoid release.
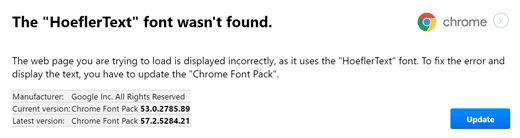
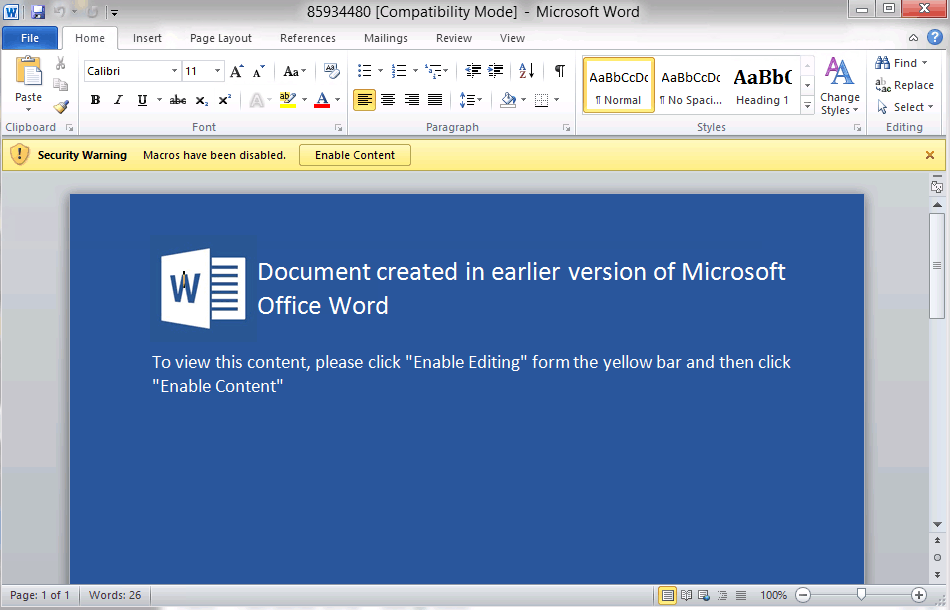
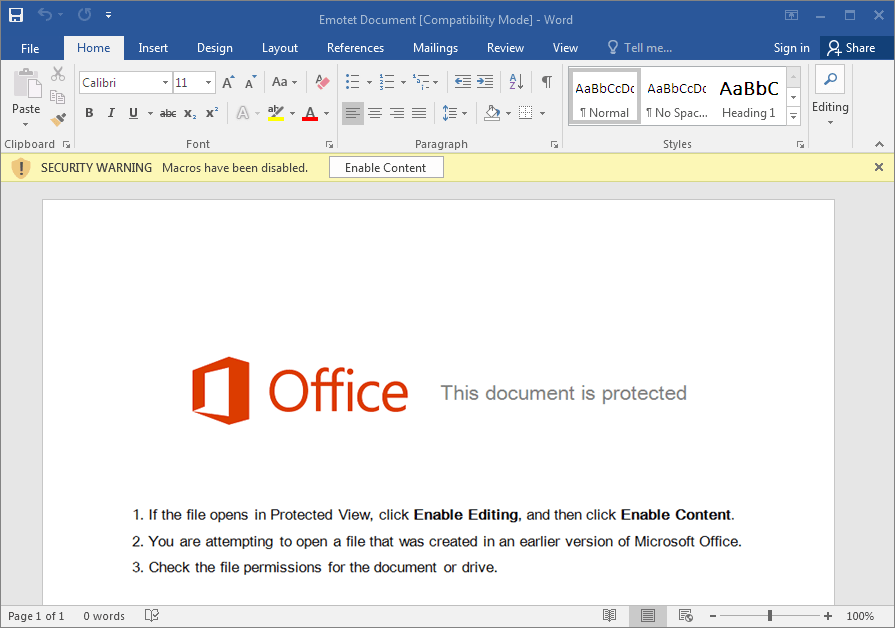
Browser hijackers can enter your device in a number of different ways, including bundled software download, malicious websites or phishing email attachments. Once they are at large within your system, they can overwhelm your browser with pop up ads, redirect you to unfamiliar search engines and download additional malware.
What do browser hijackers do?
Is chrome acting funny? Are you being redirected for no apparent reason? You might be compromised by a browser hijacker.
As touched upon already, there are many ways in which browser hijackers are able to significantly disrupt your browsing experience. Here are a few of the major symptoms to keep an eye on:
Unwanted homepage changes
Perhaps the most common symptom of a browser hijacker is your browser’s homepage changing without any user input. This is typically replaced, or the user is redirected to, a suspicious looking website that is often filled with ads and little else.
Slow browser performance
If you notice that your browser has markedly slowed down in terms of loading speeds and reactivity, or perhaps it frequently crashes despite not doing so before, it could be a sign that you have been targeted by a browser hijacker. This is generally a result of the consumption of resources from what are typically weighty and demanding malicious programs.
Excessive pop-up ads
While pop-up ads are natural from time to time, a sudden increase in these to the point where it becomes overwhelming probably means that a browser hijacker has infected your device. These will commonly appear on websites that don’t typically use ads and may lead to you to more harmful websites.
Browser settings changes
Browser hijackers regularly modify different types of browser settings such as the default search engine, new tab landing page and browser extensions. These changes will be made without your consent and are designed to control your browsing experience.
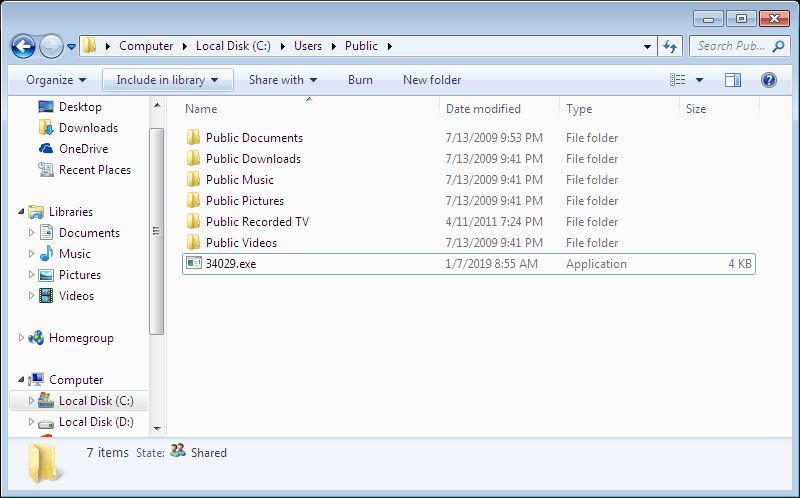
Reduced storage space
As previously touched upon, browser hijackers take up large chunks of storage space on your device with the additional unwanted programs and data that accompany them. This should be fairly obvious when you check your available storage space – if it unexpectedly and substantially reduced, that is a telling sign.
Redirected to unknown websites
The final symptom of browser hijackers is the unexpected redirection to unfamiliar, or suspicious looking websites. They have the capability to alter your search engine results pages (SERPs) so that you are unknowingly redirected to websites that will generate money for the hacker or further compromise your security.
How to prevent browser hijacking
As has been discussed throughout the article, browser hijackers can cause a great deal of frustration to the victims. Here are a series of tips put together by the team at SUPERAntiSpyware to help you avoid any potential browser hijacking attack:
Disable JavaScript
JavaScript can be exploited by hackers, who use it to execute malicious scripts on your browser. By disabling your JavaScript you are essentially preventing a large number of these attacks from formulating. This said, you should be made aware that disabling JavaScript can cause certain website features to break. Thankfully it is easy to switch on and off, so you can flip between the two where necessary.
Keep your system and software up to date
This is best practice for cybersecurity in general and will help to prevent all manner of malicious attacks, particularly those that involve browser hijacking.
Browser hijackers will often seek out unpatched vulnerabilities within operating systems or software that allow them an entry point into your device. By ensuring that you are frequently updating your operating system, browser extensions and software, you are minimizing the risk of infection.
Avoid suspicious links
It is always recommended to avoid clicking on suspicious links wherever they may arise, be it in emails, text messages or pop-up notifications and ads. These links have the potential to download browser hijackers or any other means of malicious software. It is important to use secondary communication channels to verify the source of any link that you may hold suspicions over.
Avoid pirated or free software
Another common way that browser hijackers may enter your system is when bundled together with other free, or pirated software. Once you initiate the execution of this bundle, you may be unwittingly inviting a browser hijacker to wreak havoc within your device. Software should only be downloaded from trusted and reputable sources and even then you should still review the contents of what you have downloaded. Further to this, opting for custom installation settings during the installation process gives you finer control over what you are introducing to your device.
Use robust antivirus software
One of the best steps you can take towards protecting your device from browser hijackers and all manner of malicious software is the installation of reliable antivirus software. SUPERAntiSpyware’s Professional X Edition offers protection against over a billion different threats, employing real-time AI powered detection to keep you and your device safe from attacks.
How to remove a browser hijacker
Detecting and removing a browser hijacker can be challenging due to the deceptive nature of this particular type of malicious software. This section will talk you through the steps required to get rid of a browser hijacker across a range of browsers and operating systems including Windows, macOS, Chrome, Safari, iPhone, iOS and Android.
Removing browser hijackers using antivirus software
The most reliable method for removing browser hijackers, as well as any additional malicious software that may have accompanied it, is to use dependable antivirus software such as SUPERAntiSpyware.
- Download and install SUPERAntiSpyware by following the onscreen instructions.
- Launch SUPERAntiSpyware application from your desktop.
- Perform a full system scan from the main interface. SUPERAntiSpyware will then begin scanning your device for browser hijackers and any other malware.
- Quarantine and remove infected files once the scan has completed.
- Restart your device after you have removed the infected files. This ensures that all changes will take effect and the browser hijacker will be completely removed from your device.
How to remove browser hijackers on Windows
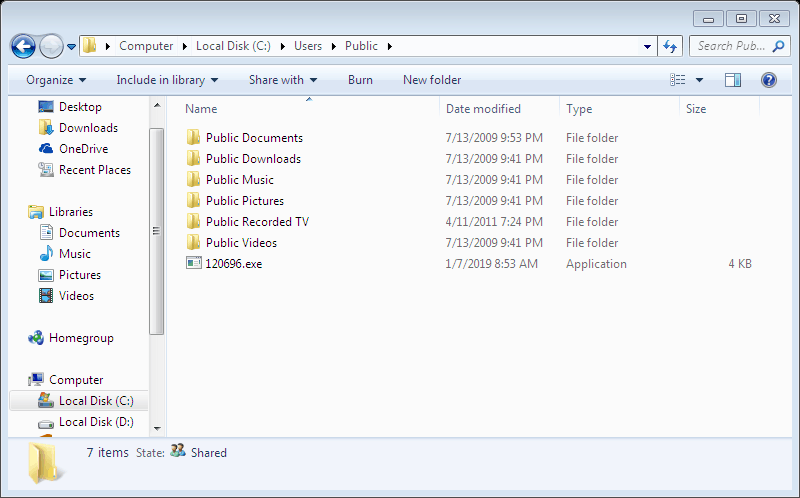
Manually removing browser hijackers from Windows is an incredibly swift process and requires very little technical proficiency.
- Select Apps & features from the Start menu.

- Carefully browse the list of apps and identify those that are suspicious and not installed by you. Once you have identified this app, or apps, then simply click uninstall and follow the onscreen instructions.

How to remove browser hijackers on macOS
To carry out this same action and remove your browser hijacker from your Mac, you also need to stop the app from running before you uninstall it. Here is how to remove a browser hijacker on macOS:
- Open Utilities from the Go dropdown of the Apple menu.

- Open the Activity Monitor from the Utilities folder.

- Locate the hijacker from the list and use the X button to stop the application from running. This will pop up a new menu, from which you should select Force Quit.

- Now that the browser hijacker is no longer running, the next step is to remove it from the device. First, open the Finder from the dock. Then, locate the application in question, hold ctrl and click on this before selecting Move to Trash/Bin.

- Finally, clear your trash bin to ensure that all traces of the harmful app have been removed from the device.
How to remove browser hijackers from Chrome
- Click the three dots on the top right-hand corner of the Chrome window and select Settings from the drop down menu.

- Select Reset settings from the menu on the left hand side of the screen and click Restore settings to their original defaults. Confirm this by clicking Reset settings.

How to remove browser hijackers from Safari
- Select Preferences from the Safari dropdown menu.
- Navigate to the General window and double check that the homepage is as you desire.
- Move across to the Extensions window and uninstall any extensions that you have not installed yourself.
- Go to the Websites window, select Notifications from the left hand menu and then deselect the option Allow Websites to ask for permission to send notifications.

- Select the Privacy window and click Manage Website Data….

- Next, select Remove All from the pop-up menu.

- Finally, click the Empty Caches option from the Develop dropdown menu on the Safari home screen.

How to remove browser hijackers from your Android phone
- Select Manage Apps from the Android Settings
- Locate the suspicious software from this list
- Open App info by clicking on the software in question and click Uninstall.
- Navigate back to the Manage Apps page and select the browser.
- Click Force Stop and then Clear data when prompted.
How to remove browser Hijackers from your iPhone on iOS
- Open the App Library and locate the suspicious app
- Tap and hold on the app itself and choose Delete App when prompted.
- Go to iPhone settings and choose your browser.
- Click Clear History and Website Data.
Conclusion
Having read this article, you should feel in a much better place when it comes to both understanding and dealing with the threat of browser hijackers. You should now understand the difficulties that they can cause, the symptoms to look out for in the interest of identification and practical tips for removing them from a range of devices, operating systems and browsers.
As stated in this article, the most reliable action that you can take to protect yourself from browser hijackers and the myriad dangers of the digital world, is to download SUPERAntiSpyware to ensure that your first line of defense is as robust as possible.
FAQs
What is a browser hijacker?
A browser hijacker is a type of malicious software that alters your browser settings without consent. These settings are changed to redirect you to unwanted websites through excessive pop-up ads which drive revenue for the hacker.
How do I know if my browser is hijacked?
The common symptoms of a browser hijacker include change of homepage, change of default search engine, slow performance, excessive pop-up ads, reduced storage space and altered browser settings.
Is there a tool that can remove browser hijackers from my device?
SUPERAntiSpyware is strongly recommended to remove browser hijackers from your device as it also deals with over a billion other threats and is powered by real-time AI threat detection, constantly evolving.
Can a browser hijacker infect my mobile device?
Yes, browser hijackers are able to infect any device that uses a web browser.




 What Are Cookies and How do they work?
What Are Cookies and How do they work?