What is PUP Malware?
This article will explore what Potentially Unwanted Programs (PUPs) are, their impact, the different types of PUPs and how they differ from Potentially Unwanted Modifications (PUMs). Read on to learn more about identifying, avoiding and removing PUPs to maintain the efficiency and security of your device.

What is a PUP?
PUPs, short for "Potentially Unwanted Programs," are a class of software halfway between malware and not malware. Unlike malware, PUPs can potentially have an actual valid use, but they are normally classified as unwanted because some of the things they do can be annoying. For example, PUPs might repeatedly show advertisements that are unrelated to the software or automatically reset certain settings.
Imagine a piece of software called something like "Easy PDF Converter" that technically works to convert PDFs, but while doing so also displays annoying advertisements. This piece of software would likely get classified as a PUP because of its annoying behavior and the fact that there are many other pieces of software that accomplish the goal without the annoying tactics.
Are PUPs Malware or Viruses?
PUPs are not considered malware because users have technically agreed to their download. Malware, on the other hand, is installed without the consent of the user and typically with malicious purpose. PUPs however are generally a part of a wider software package that has been previously installed with user permission, although often without full knowledge of what this will entail.
Malware is defined as software that has been built to harm and exploit the device on which it exists. Viruses are simply a certain type of malware that can replicate themselves and transmit to other devices.
PUPs are somewhat unique in that they do not spread like a computer virus and their consent is generally acquired from the user through checkboxes (typically hidden deep within the terms and conditions). Despite the annoying and disruptive nature of PUPs, they do not carry the malicious intent that characterizes malware and viruses. Consequently, PUPs cannot be classified as either malware or viruses.
What do PUPs do?
There are a wide range of different effects that PUPs can have on your device once they have been installed. As previously mentioned, while they are not overtly malicious, they can be incredibly frustrating and debilitating when not dealt with. Here are some common consequences of installing PUPs on your device:
- Slow down your computer: PUPs will commonly consume your system resources, which causes your device's performance to deteriorate.
- Displaying aggressive adverts: One of the most common symptoms of PUPs is that they can bombard you with repetitive, intrusive and typically irrelevant advertisements that disrupt your browsing experience. These often manifest in both pop ups and pop unders.
- Hijack your browser: PUPs can often change your browser settings, redirect your search results and add unwanted toolbars without your knowledge.
- Track your online activity: Many PUPs come with spyware components as part of their software package. While the PUP itself is downloaded with your consent, the accompanying spyware may monitor browsing habits and collect personal data without your consent.
- Alter search results: Search results may be modified to display suspicious sponsored links or adverts that attempt to direct you towards potentially malicious websites.
- Steal private information: Some PUPs possess the ability to capture sensitive data, including login credentials, that endangers your privacy.
- Obscure uninstallation: PUPs are typically difficult to remove. They will often lack normal uninstallation methods, or leave remnants that continue to disrupt your device.
What are the different types of PUPs?
PUPS come in various forms, each of which are designed to disrupt your device in different ways. Here are a few of the most common types of PUPs:
- Adware: Adware disrupts your experience by bombarding you with pop ups and banners while the program in question is running. They can often direct you to potentially malicious websites.
- Browser Hijackers: Browser hijackers modify your browser settings without your knowledge or consent. They will often redirect searches and homepages to harmful, or irrelevant, websites. This allows cybercriminals to accrue advertising revenue from increased traffic to these websites.
- Spyware: Spyware monitors your online activities while collecting sensitive information while you unknowingly browse.
- File Downloaders: These download additional software to your device without your explicit permission, often containing more PUPS or even malware.
- Toolbars: Unwanted toolbars play a role in browser hijacking, often changing your default search engine or homepage while monitoring your browsing behavior.
- System Optimizers/Cleaners: These programs claim to improve device performance by optimizing setting and removing unnecessary files. That said, they will often exaggerate the current state of play and scare you into purchasing a full version of the software, which does not deliver as expected.
What are PUMs (Potentially Unwanted Modifications)?
Potentially Unwanted Modifications (PUMs) are unwanted changes that are made to the settings of your device – often without your prior and explicit consent. These changes can be driven by malware or PUPs, often with the intention of compromising both your device's performance and security.
PUMs typically alter your system settings, browser configurations, or the Windows registry. The most common settings that are altered include default file associations, homepage settings, or security configurations. More often than not these are simply frustrating, but on some occasions, they can pose serious security risks which makes it vital to detect and reverse them as quickly as possible.
What is the difference between PUMs and PUPs?
While both Potentially Unwanted Modifications (PUMs) and Potentially Unwanted Programs (PUPs) are both capable of disrupting your computing experience, they behave differently.
The main difference between the two is that PUMs involve unauthorized changes to your device settings, while PUPs are unwanted software that causes disruptive behavior.
PUMs are actually caused by the installation of PUPs, which include malware and alter settings such as the Windows registry, or browser configurations. PUPs however, are distributed through deceptive advertising including toolbars, adware and system optimizers which may be unwittingly installed by users.
How to avoid PUPs
It is important to understand that avoiding PUPs requires both vigilance and a high level of attention when installing any new software. Here are a few useful tips to help prevent you from falling victim to any PUPs in the future:
- Always read the EULA: It is so important to make sure that you always read the End-User License Agreement (EULA) before you install any software. This is a legally binding agreement between the owner of the software and the end-user and will often mention any PUPs somewhere inside. Ensure that you look for any clauses that reference additional software and/or bundled tools.
- Download from trusted websites: Only download software from reputable and trusted websites. These can easily be identified by searching for reviews for the website/download source in questions. It is generally recommended to avoid freeware sites or unknown companies which can be common sources of PUPs.
- Choose custom installation: Always opt for custom/advanced installation settings rather than the default options. This will ensure that you are able to assess and deselect and unwanted additional programs that may be bundled together with the main software.
- Check privacy policies: Make sure that you review the privacy policies of any software that you are considering downloading. This typically provides insight into how your data may be used.
- Carefully read checkboxes: While progressing through the installation process, ensure that you carefully examine all checkboxes. PUPs will typically sneak through in pre-checked boxes that authorize alternate installations.
- Install SUPERAntiSpyware: Use a reliable anti-malware tool such as SUPERAntiSpyware to detect and remove PUPs. You can download the free version here, or enjoy our highest level of protection with the Professional X Edition.
How to remove PUPs from Windows
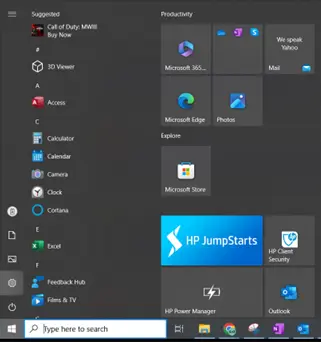
1. Click the Start button before clicking the Settings gear icon.
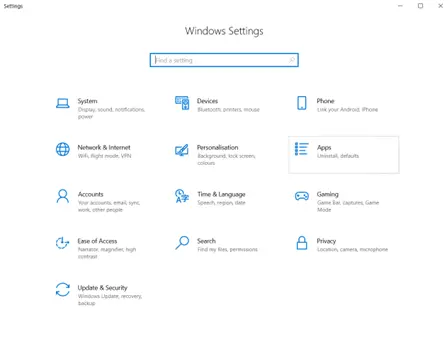
2. Select Apps from the Settings menu.
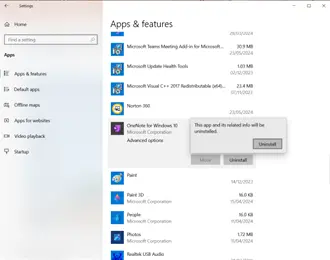
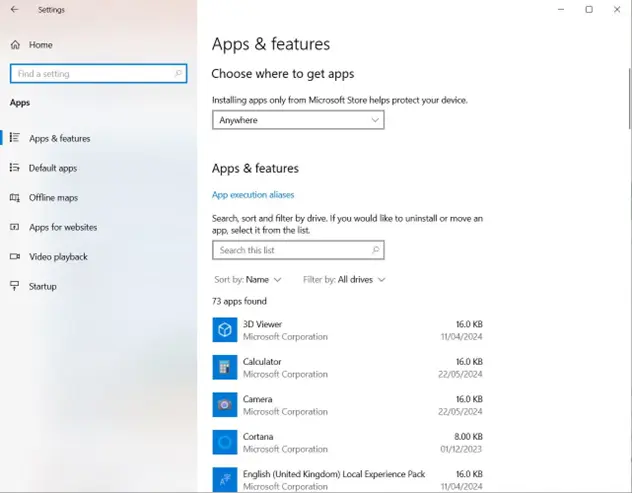
3. The Apps & Features section includes all of the apps that are currently installed on your device. Scour the list for anything that you have not knowingly installed.
4. Click Uninstall on the identified PUP (OneNote has been used as an example for the screenshot) and follow the prompts to confirm.